IT-Security Made In GerMany
Your Continuous Penetration Testing Partner!
We continuously map, monitor, and test your external attack surface — just like a real attacker would. Our platform combines automated external asset discovery with manual testing.

Continuous Penetration Testing
We’ll provide you with an advanced external attack surface management solution that is fully managed. Plus we’ll mix in expert-level hands-on exploitation.
No Setup Time — Instant Results
You don’t need to install anything, but just give us your known asset inventory, and we’ll hack it — identifying vulnerabilities before the bad actors do.
Full Coverage & Always-On
Shadow IT, third-party risks, forgotten assets—we uncover and secure everything attackers target. We’ve got your assets protected around the clock—24/7 coverage, no exceptions. Including your mobile apps.


The Smooth Part.
Once we’ve got all your digital assets, we start continuously monitoring your assets for security vulnerabilities. All discovered vulnerabilities are evaluated by our certified security analysts to save you more time focusing on your business. You will never get an unverified report!
Actionable Insights, Not Just Alerts
If we detect a vulnerability, we won’t wait — you’ll hear from us immediately. Forget about endless pages filled with false positives you have to go through manually. You’ll only get verified, realistically exploitable and as such, actionable findings.
Documentation
You’ll receive a detailed report outlining identified vulnerabilities along with clear, actionable steps to remediate them. We’ll even coordinate vulnerabilities with affected 3rd-party vendors to ensure controllable remediation.
Additional Benefits!
We understand that the security of your data is important, which is why we store every single byte in German datacentres.
Data Stored Exclusively in Europe
We take GDPR compliance seriously, ensuring your data stays exactly where it belongs—securely within European datacentres. With us, your information will always stay within the Europe, giving you complete peace of mind while staying 100% within the GDPR framework.
Small Businesses Incentive
Cyber threats aren’t just a big-business problem—small businesses are a prime target for hackers. But staying secure doesn’t have to be complicated or expensive. If you are a small business, we’ll also handle remediation processes at no extra cost, so you don’t need a security specialist at all.

What we have to offer
Affordable for any budget.
Continuous Penetration Testing
We continuously monitor your attack surface and notify you of any vulnerabilities discovered.
Penetration Tests
We also perform classic penetration tests against almost any of your assets: web apps and APIs, IoT devices or thick client apps.
Source Code Reviews
We also perform source code reviews of applications written in Java, .NET, PHP, Python, or JavaScript.
Bug Bounty and VDP Services
Do you want to run a bug bounty or vulnerability disclosure program? With more than 10 years of experience, we have you covered!
Small Business Packages
You run a small business, care about security, but have no budget for dedicated security personnel? We’re here for you, let’s talk.
Latest News
Discover our newest blog posts.
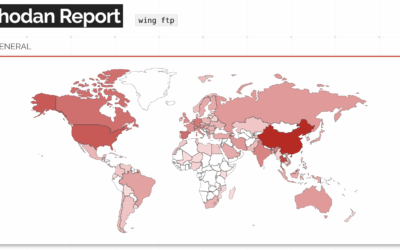
What the NULL?! Wing FTP Server RCE (CVE-2025-47812)
While performing a penetration test for one of our Continuous Penetration Testing customers, we've found a Wing FTP server instance that allowed anonymous connections. It was almost the only interesting thing exposed, but we still wanted to get a foothold into their...
SAP Emarsys SDK for Android Sensitive Data Leak (CVE-2023-6542)
In late 2023, we've discovered and coordinated a quite interesting vulnerability affecting the Emarsys SDK for Android versions 3.6.1 and below with the respective vendor, SAP. While the overall coordination process went smoothly, the security advisory published by...
WordPress GiveWP POP to RCE (CVE-2024-5932)
A few days ago, Wordfence published a blog post about a PHP Object Injection vulnerability affecting the popular WordPress Plugin GiveWP in all versions <= 3.14.1. Since the blog post contains only information about (a part) of the POP chain used, I decided to take a look and build a fully functional Remote Code Execution exploit. This post describes how I approached the process, identifying the missing parts and building the entire POP chain.